Latest Cybersecurity News:
All you need to know about cyber security
Can cybersecurity be outsourced? Since COVID-19, many companies are asking if they can get external cybersecurity help. Keep on reading to know more. Can Cybersecurity…
Removable Media Policy is the policy for removable media (such as CD-ROM, USB flash drive, floppy disk, etc.) on your campus computer. It is included…
Here are the top information security companies that rank globally. Why Information Security? Lately, the information security industry is increasing in demand and complexity. In…
Working at home is today’s new normal. However, this presents cyber risks and challenges. Boosting endpoint cyber security can help mitigate the risks involved. In…
If you are now writing an incident response plan, you may be thinking of adding an incident response plan flow chart. Well, of course, this…
Howard Schmidt is a computer crime expert and advised two U.S. presidents. In this article, we will look more into his great contribution to the…
Cloud computing and security are closely related in terms of technology and the risks that come with it. This is why in this post, we…
How can you qualify for entry-level information security jobs? The ‘Seller’s Market’ Do you know what the experts say about the cybersecurity job landscape? It…
Cyber defense remains at the forefront of the strategic plan. Since data security threats have cost millions each year. We will discuss how cybersecurity consulting…
Nowadays, there are a lot of reasons why cybersecurity matters so much. For one, we are now very reliant on our devices to get things…
Current trends in SOC automation include: More Threat Detection Tools. More automated tools are being developed to detect threats on the network. These tools are especially…
What is SOC cyber security? How does it work? What are the types and benefits of it in an organization? Let’s find the answers. What Is…
How to be an Information System Security Officer? In this post you will learn the following: What is an information system security officer? What are…
Let’s take a look at the topics covered in this article on cybersecurity fundamentals. Read on to learn more. Cybersecurity Fundamentals What is cybersecurity? Cybersecurity is the practice of protecting information, devices, and systems from attacks. It is a constantly evolving field that centers around protecting data and systems from being compromised by hackers, viruses, … Cybersecurity Fundamentals: Introduction to Cybersecurity Read More »
Below are workplace security measures that employees should follow: Provide Clear Guidelines If your organization is allowing employees to choose their own devices, provide clear guidelines about what kinds of devices are acceptable and make a list of approved applications that can be used on that device. Use Two-Factor Authentication Require all remote users to … Workplace Security: How to Deal with Remote Work Risks Read More »
Fortress Information Security is one of the biggest information security companies. Why? For one, they are known to help other companies in risk management. They also help protect the critical infrastructures of the US. And these include: financial services like banks transportation defense So, to know more about Fortress Information Security, read on. Fortress Information … Fortress Information Security Read More »
Incident response plans vs disaster recovery plans are often thought of the same. But actually, they are not. Each plays a different role in cybersecurity, especially in times of incidents. So in this article, let us discover the difference between an incident response plan vs disaster recovery plan. What is an Incident Response Plan? An … Incident Response Plan vs Disaster Recovery Plan Read More »
What is an information security risk? Also, how can you avoid this? Read on to learn more. What Is an Information Security Risk? An information security risk can result in damage to the IT systems. So, it is something that we should avoid. So, we can secure our information. Otherwise, we can face loss. In … Information Security Risk: Full Definition Read More »
An EDR solution is designed to detect and respond to advanced attacks targeting your company’s endpoint devices. EDR products can automatically detect malicious applications on endpoints, stop processes communicating with remote hosts, quarantine compromised endpoints, and remove any malicious code from them before it can infect other devices. The best EDR solutions can provide more … What is Endpoint Detection and Response (EDR)? Read More »
The NIST detect respond function consists of operations that should be carried out in response to an identified cybersecurity problem. The ability to contain the impact of a possible cybersecurity issue is supported by the Respond Function. In this post, let us know more about this function among the five functions of the NIST cybersecurity … What is the NIST Detect Respond? Read More »
Here are the trending topics in cyber security. Trending Topics in Cyber Security 1. Integrating AI with cybersecurity Many take interest in integrating AI with cybersecurity. With a combination of data mining and artificial intelligence, this system can create a movement that will confuse its opponent. With this system in place, cybersecurity could be a lot … Trending Topics in Cyber Security Read More »
There are so many growing threats for businesses. Thus, they need corporate cyber security. These threats include: unauthorized transactions customer data theft adding fake employees fund transfers Cybercriminals’ attacks companies using different ways. They use phone calls, phishing, and social media. Besides, these criminals send seemingly common emails. They make it appear like emails from … Top Effective Practices for Corporate Cyber Security Read More »
What are the principles or prin of information security? Also, why is it important to learn about these? To sum up, information security protects information. And we need to do so today. News about hacks and breaches happen. So, we should do something on our part. How can the prin of information security help us … Prin of Information Security Read More »
What is a cybersecurity breach? A cybersecurity breach is the result of unwanted access to data, apps, or networks. This happens when someone bypasses security protocols. But, you may have also heard of data breaches. Well, is it the same with a cybersecurity breach? To illustrate, imagine a burglar. The moment he climbs through a … Cybersecurity Breach: Full Definition Read More »
When it comes to cybersecurity careers, there is a lot to choose from. So this post will guide you into choosing that cybersecurity career path by heart. The Growing Need Of Cybersecurity Professionals Aside from the advancement of technology, there also comes the growing sophistication of threats and cyber-attacks. This is why cyberattacks are constantly … Cybersecurity Careers: How Can I Choose Wisely? Read More »
Here are the basic cyber security strategies that you should try. Cyber Security Strategy Tips 1. Keep your operating systems, applications, and web browsers updated. It is important to keep your operating systems updated because the updates often patch security vulnerabilities. It is a crucial step to protect your information from being hacked. 2. Keep software and … Cyber Security Strategy Tips Read More »
Cloud computing in cybersecurity can be useful to store and analyze large amounts of data. This allows businesses to analyze the patterns in data to see if it provides any useful information for cybersecurity. What are the advantages of using cloud computing in enhancing cybersecurity operations and services? Cloud Computing in Cybersecurity For example, a … Cloud Computing in Cybersecurity Read More »
Just how serious healthcare cybersecurity is in the healthcare industry? According to Becker’s Hospital Review, approximately more than 5 Billion Dollars costs the healthcare industry in a year. More than 27 million patient records attacked in a year, with an average of at least one health data breach per day as per the Breach Barometer … Healthcare Cybersecurity: Share For Everyone’s Protection Read More »
Cybersecurity is a major concern even for cloud home users. Learn these basic cybersecurity hacks that you must try on your home. Basic Cybersecurity Hacks for Home Use You will learn how to keep your home and devices safe from malware, hacking, and other dangers. There are also tips on how to protect your privacy … Basic Cybersecurity Hacks for Home Use Read More »
If you’re wondering if your systems are secure, an information security audit is a great way to uncover the vulnerabilities in your systems. At first, you might feel uncomfortable from an information security audit. It exposes all of your systems and strategies. Yet, it’s totally worth it. Audits will help you eliminate risks before they … What Is An Information Security Audit? Read More »
Several Pointers For Computer Security is vital to fighting the continuing increase in danger to computer security. Tip # 1-A choice for hackers is you. We seem to be in continual danger. Besides, the threat is real-for both personal and mental well-being and the status and prestige of the organization.In addition, computer security is an … Pointers For Computer Security Read More »
With the rapid growth in technologies, cybercrimes also increase. So, the cybersecurity business becomes in demand also. So let us learn some tips for starters in the cybersecurity business. Cybersecurity Business In 2020 The demand for cyber professionals or services is really high and pricey. That some companies are willing to pay the average amount … Cybersecurity Business Tips For Starters Read More »
We are now living in a time where great cybersecurity content is freely available on YouTube. Take a look at the best cybersecurity YouTube channels. Courses and training are not the only ways to learn about this awesome topic – cybersecurity. You’ll find awesome cybersecurity videos on YouTube without spending a single penny. In fact, … Best Cybersecurity YouTube Channels Read More »
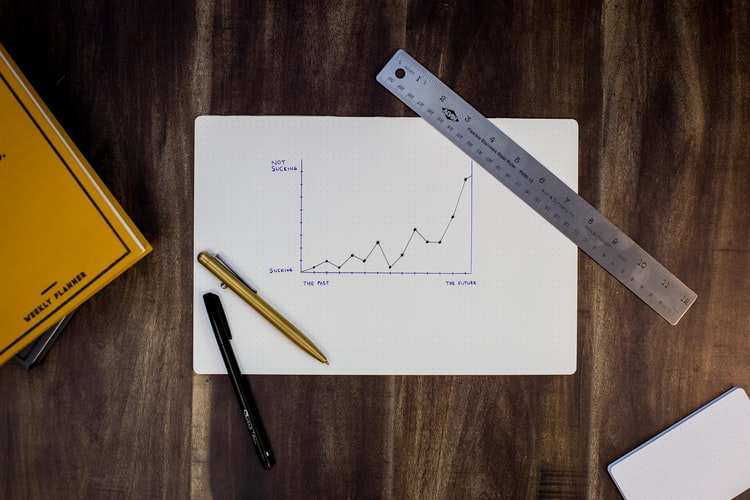
Are you in the cybersecurity business? If so, how can you attract potential customers and grow cybersecurity sales? In this post, learn helpful tips that can help you do so. Tips in Growing Your Cybersecurity Sales Here are some helpful tips that can help you raise your company’s cybersecurity sales. Don’t Confuse Customers You should … Tips on How to Grow Your Cybersecurity Sales Read More »
News feed from the web
all about cyber security
A cyber security expert says it comes down to understanding what type of device your child is using, when keeping…
Financial Service Cyber Security Market Capacity, Production (K Units), Revenue (Million USD), Price (USD/Unit) and Gross Margin (2021-2027) | IBM, ……
Cyber Security Analyst. Job ID: 218521. Location: CHANTILLY, VA, United States Date Posted: Jun 14, 2021. Category: Cyber Subcategory: … read…
NEW ORLEANS – Cyber attacks are a constant occurrence. Even more worrisome, they have become more sophisticated, more destructive, and…
Leading cyber/data/privacy partner Patrick Van Eecke joins Cooley in the firm’s Brussels office. read source
Bermuda has introduced the Operational Cyber Risk Management Code of Conduct (Code) which applies to all Bermuda registered insurers, insurance ……
In the online public awareness survey conducted by the Cyber Security Agency of Singapore (CSA) last December, two-thirds of the…
The U.S. Commercial Service’s Cyber Security Virtual Fair is designed to spark conversations between innovative U.S. Cyber Security solution … read…
Ahmedabad: An elderly businesswoman from Ahmedabad, Gujarat lost nearly Rs 1 lakh to cyber fraudsters while trying to get a…
SEPA hasn’t yet detailed how cyber criminals were able to break into the network to deploy ransomware and the investigation…
Amar Singh, CEO of Cyber Management Alliance, backed the idea of apprenticeships to build up UK-wide capability. “It’s a pipeline…
The past month in cyber security has been dominated by one story: a huge cyber-espionage campaign against the US government.…
The research report presents exclusive information about how AI in Cyber Security will grow during the forecast period of 2020-2026.…
The Cyber Monday Too Faced Mystery Grab Bag is available now! read source
Start of school year cyber drama continues. As if the lengthy debate over how to reopen schools wasn’t enough of…
Cyber weapons — often deployed by hostile states — are becoming extremely sophisticated, and governments struggle to contain them. Shorting ……
With the exception of “a few MIAs,” all of Pleasant Valley’s cyber students are now receiving instruction, Superintendent Lee Lesisko…
Kendall Park resident Sudeeep Khetani, 34, was taken into custody on Tuesday for the “cyber harassment” he allegedly conducted between…
“Cyber litigation is one of the fastest-growing areas of civil litigation in the United States,” Mr. Yannella said. “What we…
The national cyber director, a Senate-confirmed position, could play a critical role as federal agencies grapple with the depth and…
Next week sees the arrival of the new 8-bit ninja platformer Cyber Shadow on the Nintendo Switch eShop. If you…
He adds that cyber liability is not typically included under professional indemnity insurance and warns that PI should not be…
The purchase of threat hunting specialist Root9B expands the scope of the cyber practice at Deloitte & Touche LLP, which…
By adding an experienced cyber veteran to the team, Nordic will better enable clients to secure, optimize and evolve their…
Cyber Risks for Educational Institutions Usually, the networks and systems of an educational institution are not as strong and secure…
The statistics portray the rising incidences of cyber attacks in the growing era of technological advancements. Enterprises from both public…
Ambience Mall, DLF Cyber Park and adjoining areas will also be affected by the shutdown. “The shutdown will force the…
Vulcan Cyber said it surveyed more than 100 security and IT leaders about the current state of vulnerability management at…
Every one of the efforts in court or with state officials since Election Day to overturn the results of the…
Broadband Conversation, hosted by FCC Commissioner Jessica Rosenworcel, features a conversation with Congresswoman Suzan DelBene who … read source
For the first time, global hoteliers will come together virtually today to attend CYBER HITEC, an online hospitality technology conference…