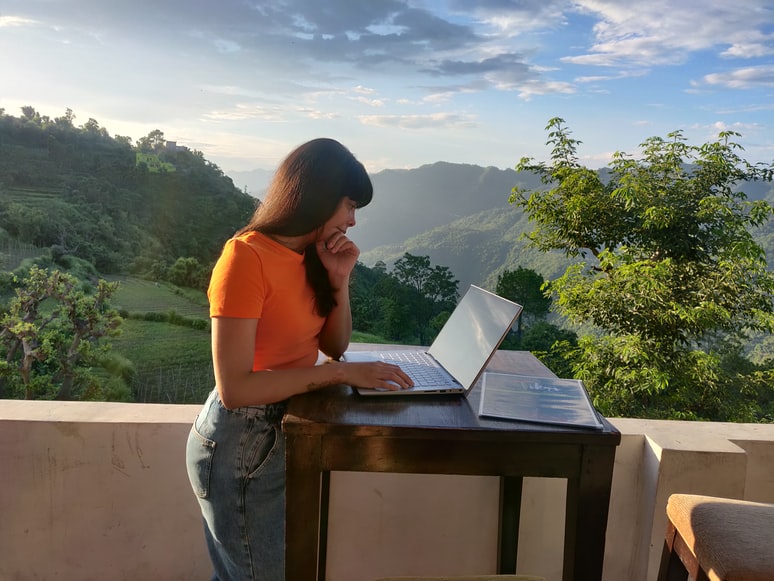
Remote working security is an important security concern for many organizations. It is also a growing trend, with many employees working from home, from different locations, and from outside the office.
The security of remote working is often misunderstood. There are many myths about remote working security and these can cause organizations to not secure their remote workers properly. The lack of security can result in sensitive data being accessed by unauthorized people.
Although some remote work is secure and can be appropriate in some situations, there are often some issues that need to be considered and overcome.
How to Manage Remote Working Security
Here are tips on how you can manage remote working security:
Data encryption
Data encryption is the main concern for remote working security. Many remote workers often use public networks, such as coffee shops, airports, and hotels. This makes it easier for unauthorized people to steal data from a network, as they can just pick up the data from the wireless network.
Although data encryption can be useful to protect against this, it is not always feasible. If the unauthorized person manages to access the wireless network, they may be able to access the information that on encryption. If a hacker was able to access confidential information about your organization through the wireless network and then encrypt it; you may have no way of knowing if any of your data has been taken and encrypted without decryption.
Encryption is a very important part of remote working security. Make sure to encrypt data and only be decrypted through a password or key. This means that while data encryption is used, it can also be used to protect against unauthorized access to data. Data encryption should also be used on all mobile devices.
Physical security
Physical security is another important aspect of remote working security. It is easier for someone to access your sensitive data through a remote connection than through a physical connection. Although many remote workers use encryption, this does not protect against someone stealing the information from the device itself. For example, if an employee left their laptop in an airport or coffee shop, it could have easily been stolen.
Therefore, without encryption, there are still several ways in which someone could access your data from a laptop or portable device. They may be able to access the physical device and look at information stored on it. They may also be able to use social engineering techniques to get information about the organization and its employees and then use this information to access other devices and networks within the organization. Therefore, you must consider physical security into account when you design your remote working security procedures.
Social engineering attacks
Many people often forget about social engineering attacks when they are designing their security procedures. Social engineering attacks are often more successful than technical attacks because they rely on human interaction, which can be harder to detect than technical attacks.
Therefore, social engineering attacks are very effective in getting sensitive information about an organization and its employees at an early stage. Once they have this information they may then use it to exploit other parts of an organization’s security system using other techniques such as technical attacks or physical attacks such as phishing emails or spoofed websites.
Therefore, it is important when designing the remote working security procedures that you take into account social engineering attacks too and make it easy for your employees to report them if they do occur so that you can take action against them before any real damage occurs.